Cybersecurity is accelerating.
Even if we don't know this, we feel it. CVEs keep growing year by year. So does Time to Exploit. And AI is giving everyone, no matter which side of the law, the room to move faster and more destructively.
That's the context in which we wrote this report.
Telecom is arguably the most important industry in our society. There's nothing it doesn't touch. And not only are we dependent on it, telecoms contains troves of priceless data.
You can only defend if you know the map. And that's why we've analyzed 591 domains belonging to European Telecoms, totaling over 50,000 exposed, public assets. Our goal is to give CISOs and CTOs a data-driven perspective on the attack surface exposed to cybercrime and how their organizations compare to industry peers.
Download the Source Data and PDF
Receive a copy plus the anonymized data set in your inbox
Executive Summary
Our analysis revealed three major security gaps in the European Telecom sector:
- 37% of HTTPS connections use invalid or outdated SSL certificates, creating opportunities for man-in-the-middle attacks and data interception. These are fundamental security hygiene failures that persist due to incomplete attack surface visibility. This figure is significantly inflated by a small number of large operators with extensive invalid certificate counts; excluding the top outliers, the figure is closer to 17%.
- 47% of web servers expose sensitive version and software information, providing cybercriminals with reconnaissance data to quickly identify and exploit known CVEs without additional effort. As with SSL, a handful of large operators with high exposure rates skew this figure upward.
- 1,452 critical assets, including API endpoints, email servers, admin dashboards, VPNs, and portals, show concerning weaknesses, with webmail systems exhibiting the worst posture: 12% exposed configurations and 4% with SSL bad practices.
These findings carry three significant implications for European Telecom leadership:
- Visibility gaps create undefendable attack surfaces. If security teams don't know what assets exist, they cannot protect them. This mirrors industry research showing 37% of enterprise attack surfaces are unknown—a foundational weakness that makes all other security investments less effective.
- Traditional security approaches cannot match threat velocity. With Time-to-Exploit now approaching -1 days (meaning zero-days are exploited before patches exist) and CVE disclosures up 16% in 2025, annual or quarterly penetration tests are fundamentally inadequate. The attack surface changes faster than periodic assessments can capture.
- Critical business assets face disproportionate risk. The assets most vital to operations, such as customer portals, network management systems, and administrative access, show security weaknesses that could result in business disruption, regulatory penalties, and reputational damage.
Luckily, the solutions to these problems are already available out there and ready to be implemented:
- First, organizations need extensive Attack Surface Management (ASM) to maintain real-time visibility of all exposed digital assets, including third-party and supply chain connections, eliminating blind spots that attackers exploit.
- Second, by using autonomous, AI-powered penetration testing with event-driven triggers for code changes, infrastructure updates, and new threat intelligence, vulnerabilities are discovered and validated at the speed of modern development cycles.
- Third, with automated detection and correction of basic security hygiene issues, organizations can resolve low-hanging fruit that significantly reduces attack surface risk with minimal investment.
The results of this study suggest that there is an increased risk of exposure to cyberattacks across European Telecom, and it is prudent to consider implementing preventive measures and incentivising collaboration with security researchers. Organizations that embrace continuous, autonomous security testing will discover, prioritize and remediate vulnerabilities before they become breaches. Those who rely on periodic assessments will continue to appear in breach headlines.
Methodology
To conduct this analysis, we’ve used our proprietary recon tool. This tool allows for a passive, non-intrusive reconnaissance of an organization's exposed digital infrastructure, using only its main web domain.
The tool can identify:
- The total number of exposed digital assets (subdomains, applications, IPs, and others);
- Types of web servers, services, technologies, and integrations;
- Server information exposure and configuration of secure digital certificates.
Additionally, we’ve also analyzed active recon and testing data from our hacking agent, Hackian, to give you more context on vulnerability trends regarding Telecom companies.
In addition to quantitative attack surface analysis, this report incorporates insights from in-depth interviews with cybersecurity leaders at European Telecom organizations. These conversations provide context on the real-world challenges of defending Telecom infrastructure, current threat patterns, and the gap between industry best practices and common practices.
Notes and Important Limitations
For the passive, non-intrusive scans conducted, our tool performed a preliminary reconnaissance of the attack surfaces in question. This means that the tool only accesses information available in various public databases and via legitimate access to various web domains, without resorting to any active testing. In other words, the tool is non-intrusive. Furthermore, this analysis only reveals digital assets exposed on the web, which does not include all digital assets of an organization. Missing are, among others, mobile applications, internal networks, and assets.
Thus, the results presented here are limited and may differ from the actual situation, as they result from an analysis restricted to a very limited period. Generally, attack surfaces are larger and present more vulnerabilities. Therefore, the scenarios presented can be considered as “best-case scenarios”. A more in-depth and realistic analysis could be carried out with the proper legal authorization from the responsible parties of the web domains under study.
Finally, all listed domains were obtained through public databases and via legitimate access to various web domains.
Introduction
This report was created using public-facing data sources, opinions collected from industry experts, and data from the external attack surface of nearly 600 European Telecom companies. Our goal is to provide CISOs and security practitioners with information on the state of the industry, so they can understand risks and compare their own efforts with what’s being done in the industry as a whole.
Cybersecurity Landscape in Telecom
Recent years have seen more attacks on some of the biggest Telecom companies in Europe. Free and Free Mobile was fined over €40 million for GDPR violations after a leak of over 20 million customer records. SFR/Altice suffered three different breaches in 2024. And over 6 million customer records from Bouygues were stolen in August 2025. Telecom companies manage vast amounts of sensitive customer data and critical communications infrastructure, making them prime targets for ransomware and espionage, and often operate legacy systems, as we’ll see later in this report.
This follows the overall trend for European businesses. One in eight faces cyberattacks annually, with enterprises facing the biggest risks, and often without knowing where. Reports by Censys reveal that somewhere between 40 to 60% of attack surfaces are unknown, which is a weak point to start with. If you don’t know where an attack can come from, it’s impossible to defend yourself.
This assessment is corroborated by security practitioners on the front lines. Laura Iglesias, Head of Cybersecurity for European Markets at Vodafone, noted a rise of highly skilled threat actors going after critical infrastructure and supply chains, whether for espionage or just to cause disruption. But while it may seem there’s no break in sight, Przemysław Dęba, CISO at Orange Poland, shares an optimistic vision shared by other Telecom CISOs: Continuous exposure to real-world attacks keeps the region's defenders sharp and adaptive, and reinforces that public-private collaboration and technological openness remain essential.
Telecommunications are critical to modern life. Disruptions in, say, internet coverage can lead to widespread damage. A recent example is the outage caused by an attack on Orange Spain, where 50% of their internet traffic was disrupted for several hours. While the disruption didn’t last long, it begs the thought of what would happen if disruption was widespread.
Continuous exposure to real-world attacks keeps the region's defenders sharp and adaptive
To add to this, there’s the risk from connections with third parties, which only increases the risk of cyberattacks. TalkTalk is the most recent example, where 2 million records were leaked after a criminal exploited a third-party tool. Ever-increasing attack surfaces, combined with the attack vectors offered from unsecured and untested third parties, paint a dire picture for European Telecom.
Supply chain attacks have evolved beyond traditional software compromise. Terje Jensen, SVP, Head of Global Business Security, Telenor, mentions the rise of insider threats coming from Telecom partners and how it’s affecting their supply chain.
Additionally, there’s an increase in the number and impact of CVEs being disclosed. While this increase is in part due to more researchers sharing their findings, it’s also a consequence of the presence of software in all aspects of our lives, combined with the increase in the speed of writing and deploying software caused by coding agents. The number of CVEs published in 2025 increased 16%, and as if this wasn’t concerning enough, sources like Mandiant have revealed that Time-to-Exploit, which tracks the average number of days between a patch release and active exploitation, has dropped to -1 days for the first time. This is also corroborated by research from Zero Day Clock, showing 54% of exploited CVEs in 2025 were 0days, and median Time-To-Exploit was -8 hours. All of these trends are expected to accelerate as more capable models like Claude Mythos continue to improve and find vulnerabilities.In other words, zero-day vulnerabilities are now being actively exploited in the wild before a patch is even available.
It’s in this critical context that we write this report. Our goal is that this report helps you understand how Telecom companies are doing and what threats they face, so you can analyze your current practices and adapt accordingly.
Analysis of Digital Exposure
In this section, two preliminary and superficial analyses of the exposed digital infrastructure associated directly or indirectly with these companies are presented, to obtain an initial assessment of the potential risk of exposure to cybercrime.
Through these analyses, it is possible to quantitatively and qualitatively evaluate the attack surface of various organizations, that is, the digitally exposed assets that are susceptible to cyberattacks. This provides a general idea about the security posture of the digital infrastructure.
Type of Organizations Analyzed
Firstly, to paint a picture of the kind of companies we’re analyzing, it’s important to mention what companies compose the sample.
As mentioned, 591 companies were analyzed. 14% of these companies have over 5,000 employees, and about 59% have between 201 and 1000 employees. We only analyzed Telecom companies in the European Union, United Kingdom, Norway, Iceland, and Switzerland, with a minimum of 200 employees. If your organization falls within these brackets, the vulnerabilities we've identified are statistically likely to exist in your infrastructure.
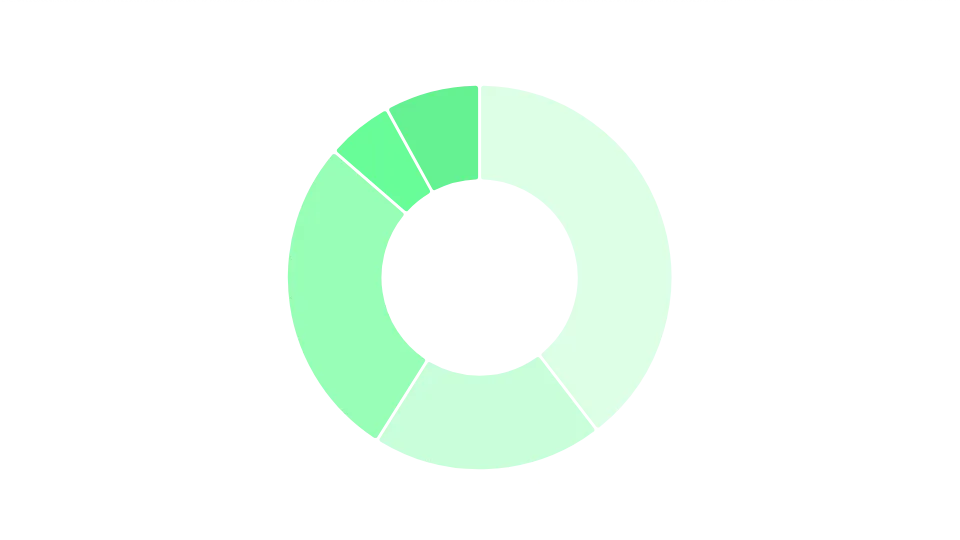 Image 1 - Distribution of companies by number of employees
Image 1 - Distribution of companies by number of employees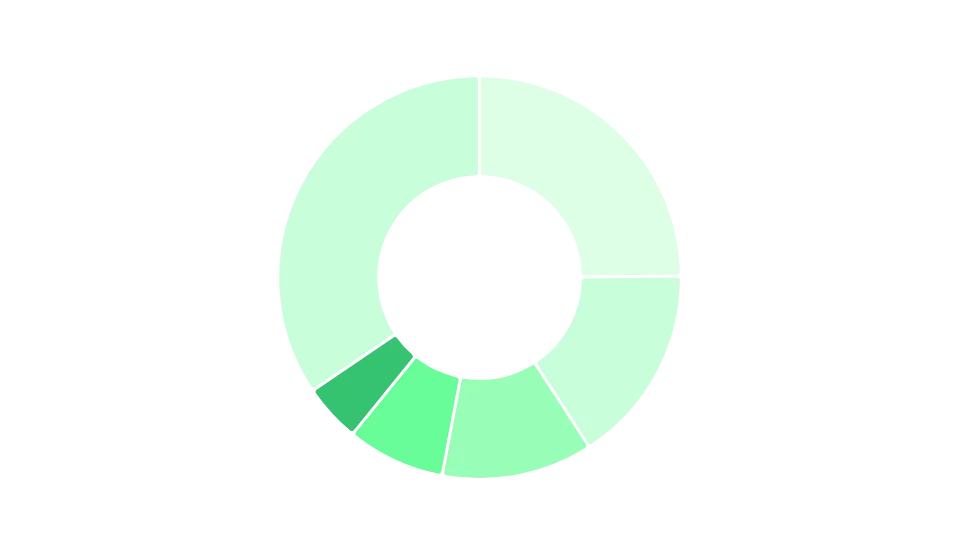 Image 2 - Distribution of companies by country
Image 2 - Distribution of companies by countryRegarding revenue, most companies fall in the 100M to 1B bracket (45% of sample), followed by the 10M to 100M bracket (40%). 12% of the sample grosses over USD 1 billion per year. The United Kingdom, France, and Spain are the most represented countries, respectively.
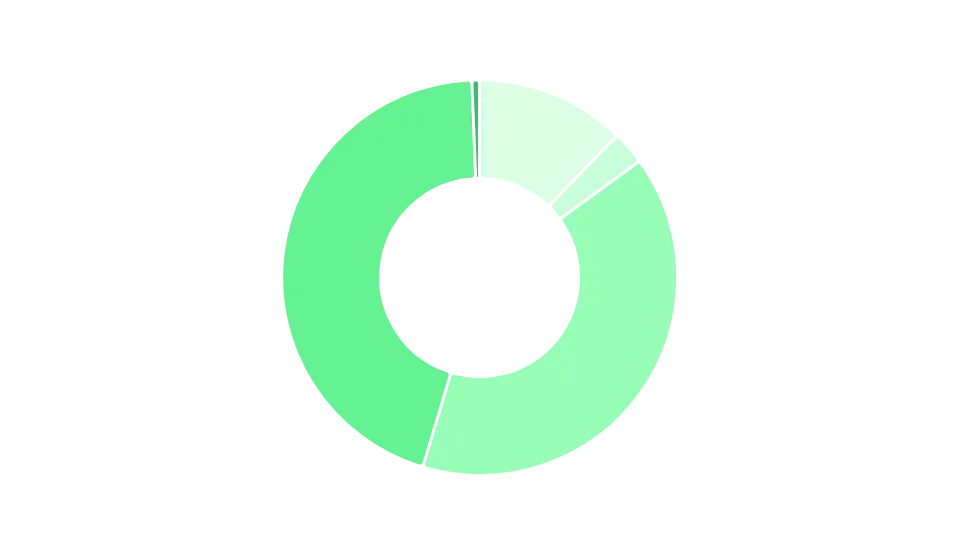 Image 3 - Distribution of companies by yearly revenue
Image 3 - Distribution of companies by yearly revenueThe diversity of our sample reflects an important reality: "Telecom" is no longer a monolithic category. Modern Telecom organizations operate far beyond traditional voice and data services.
We see insider threats, but both insider threats within ourselves as a Telecom but also insider threats from Telecom partners — that is also growing quite a lot. Supply chain is also coming up as a big increasing threat. [...] We are managing multi-technology networks. Some of the 2G stuff for example is more than 30 years old and we are still providing seamless services across a number of technologies. And some of these are actually imposed from the regulation point of view — something we need to maintain.
This complexity explains why even mid-sized Telecom companies in our sample average 85 exposed assets. Each business function, partnership, and customer touchpoint adds to the attack surface. For security teams, this means defending not a single perimeter, but multiple overlapping ecosystems with varying security maturity levels.
Size of the Exposed Digital Infrastructure
Initially, we analyzed the digital assets of these organizations, providing an insight into the size of their digital infrastructure. For this report, any exposed domain or subdomain is considered an asset. We analyzed all assets under the main domain of each organization.
A total of 591 main web domains were analysed, resulting in the identification of 50,283 exposed assets. We found that each domain has, on average, 85 exposed assets.
Breaking this down, we notice that most companies have between 1 and 10 assets (40% of the sample), with 42% having between 11 and 100. Only 3% exceed 500 assets. It’s also interesting to note that companies with 10,000 or more employees heavily skew the sample, as they average 371 assets, while the average across the entire data set is, as mentioned, 85 assets. It’s also clearly noticeable that as the employee count increases, so does the number of assets. This trend is also visible when breaking down the data set by revenue bracket.
From this analysis, it’s easy to conclude that even mid-sized Telecom companies have a substantial attack surface that cannot be effectively secured through manual processes alone, as each asset requires manual, repetitive security work.
This problem only gets trickier the bigger the organization. Enterprises with 10,000+ employees average 371 assets, which means exponentially more complex security challenges. Larger attack surfaces have more interconnections, more third-party integrations, and more potential lateral movement paths for attackers.
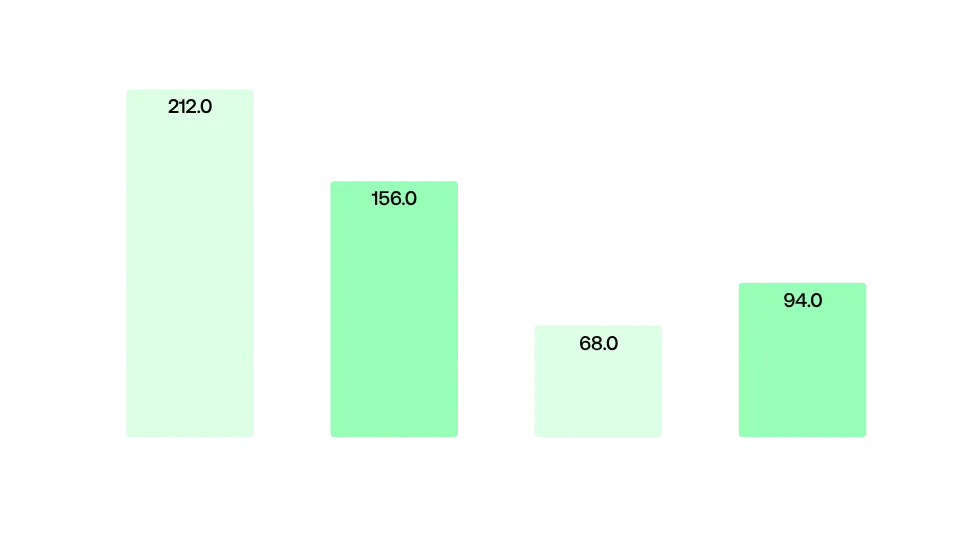 Image 4 - Distribution of companies by number of assets on their main domain
Image 4 - Distribution of companies by number of assets on their main domain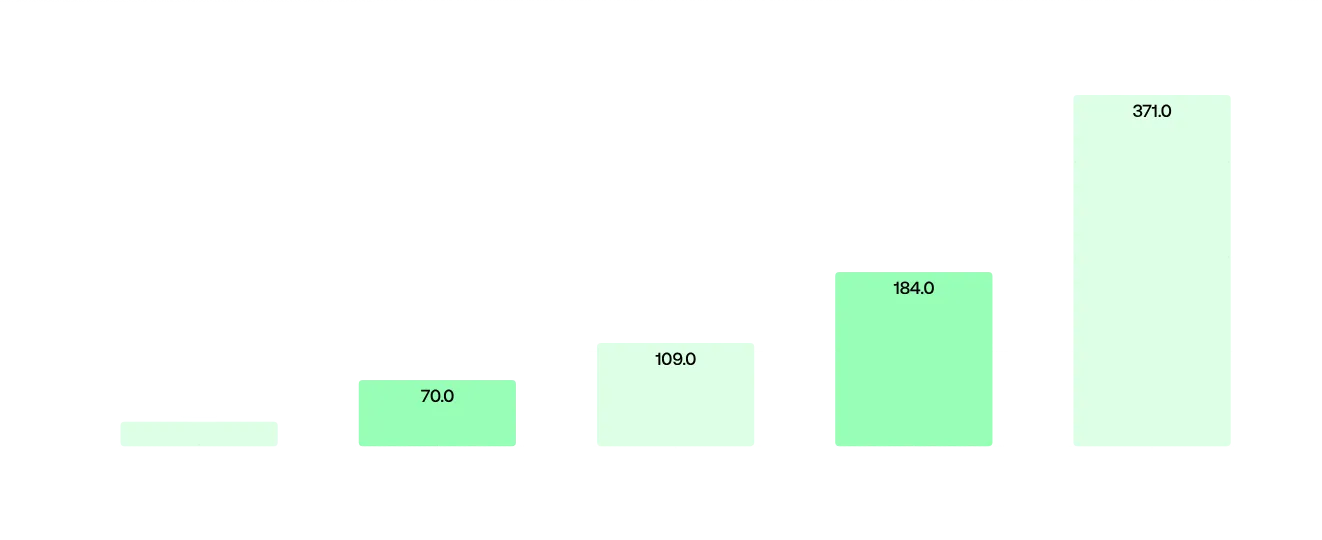 Image 5 - Average number of assets by number of employees
Image 5 - Average number of assets by number of employeesTypology of the Exposed Digital Infrastructure
A qualitative analysis of the exposed digital assets was also conducted to evaluate the attack surface from the perspective of services, servers, technologies, integrations, and even the most commonly used products by organizations.
Nginx is the most widely used technology, which is consistent with other analyses we’ve done. It’s a versatile, widely deployed web server and reverse proxy. We’ve also found other common technology choices such as Apache, Cloudflare, and AWS Cloudfront, widely used across every industry.
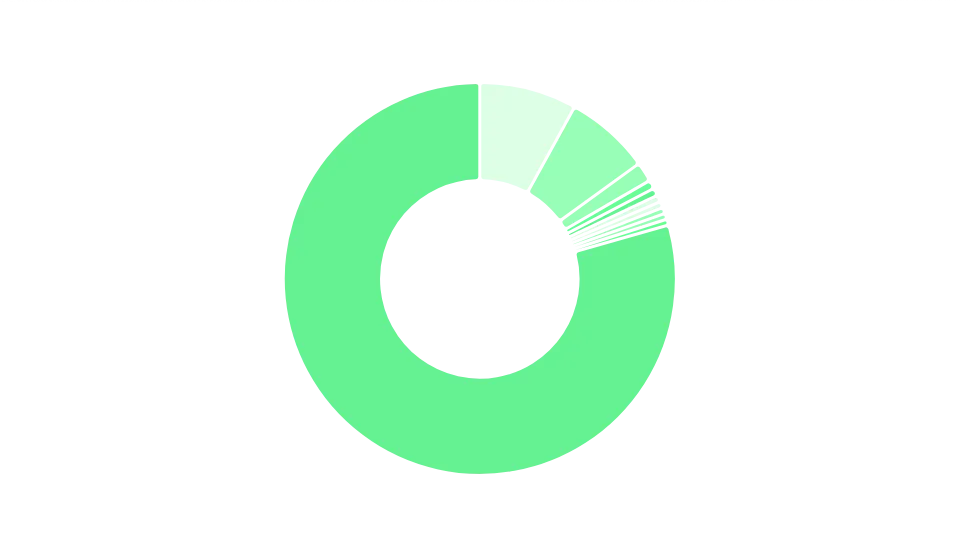 Image 6 - Distribution of services used
Image 6 - Distribution of services used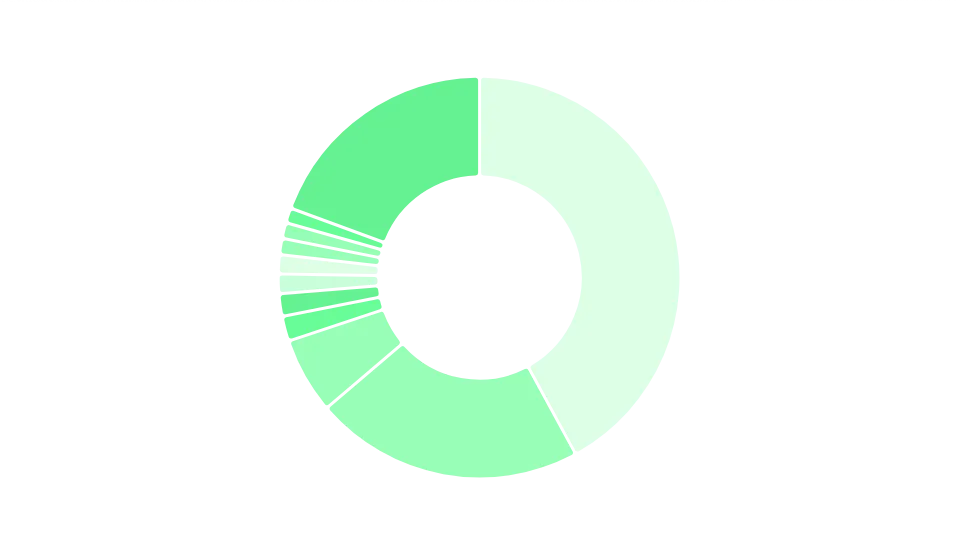 Image 7 - Distribution of technologies used
Image 7 - Distribution of technologies usedWhen it comes to web servers, Nginx dominates, representing 48% of web servers analyzed. Apache follows with 18%, and Cloudflare with 7%. These are the most common options we observe, and together they account for nearly three-quarters of web servers analyzed.
Using common choices brings advantages and disadvantages: while on the one hand they're proven and, if there's a vulnerability, a fix should be quickly rolled out, the fact that they're so widespread can lead to chain reactions, as we've seen from the impact of the recent Cloudflare downtime events.
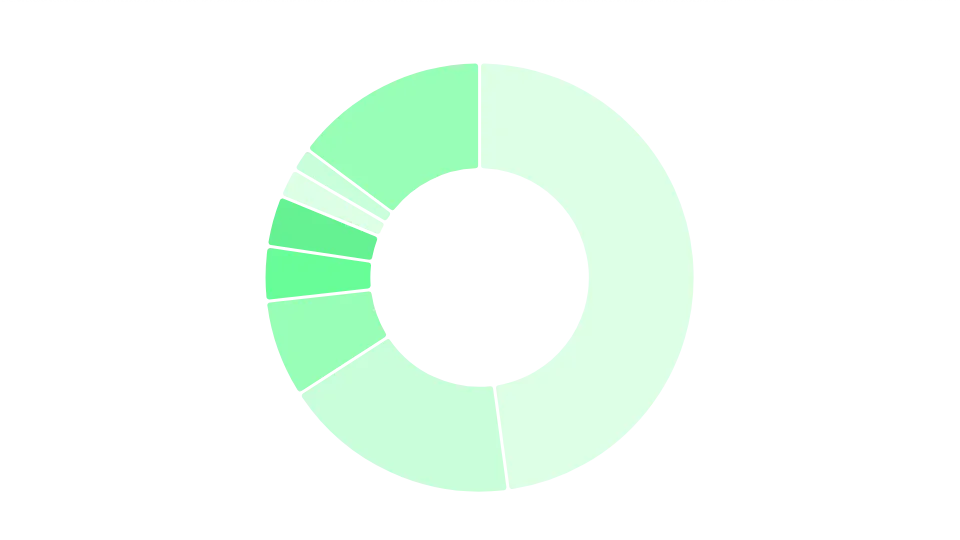 Image 8 - Distribution of web servers used
Image 8 - Distribution of web servers usedDespite the massive difference in the average number of assets, there isn’t a big discrepancy in the technologies used. The most common web server technologies, regardless of size, are Nginx, Cloudflare, Apache, IIS, and Firewalls like Akamai, suggesting that as Telecom organizations grow, the underlying tech stack remains the same.
Security Posture in Exposed Assets
Regarding the security posture associated with the exposed digital infrastructure, it was possible to analyze the use of valid SSL digital certificates and the exposure of information from web servers.
In terms of SSL certificates, it was found that 37% had either invalid or outdated certificates, following bad practices. Such a situation could allow an attacker to intercept traffic when connected to the same network, enabling attacks such as eavesdropping and man-in-the-middle. This figure is heavily influenced by a small number of large operators (notably Swisscom and Free.fr) with very high counts of invalid certificates; excluding these outliers, the rate is closer to 17%.
This lack of updates often happens due to a lack of visibility on their attack surface, which leads to these weaknesses going unnoticed. This is corroborated by the fact that companies with more than 500 assets, and therefore more complex attack surfaces, show a worse posture, with 33% of connections showing bad practices. Companies with fewer assets show a better posture, with those having fewer than 50 assets averaging 14%, and those with fewer than 10 assets averaging 8%.
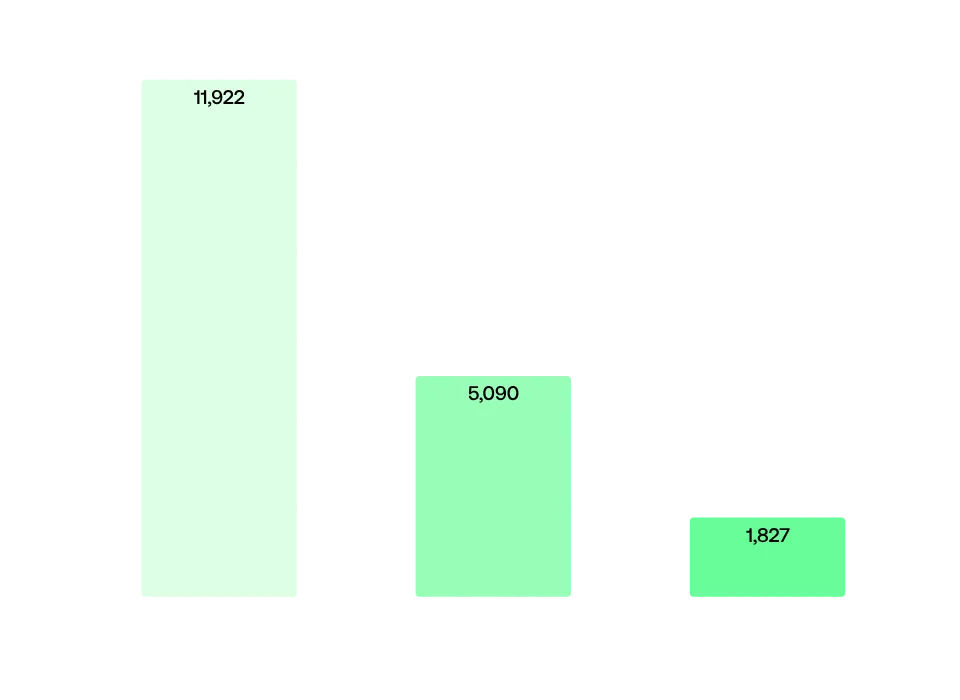 Image 9 - Types of SSL certificates
Image 9 - Types of SSL certificates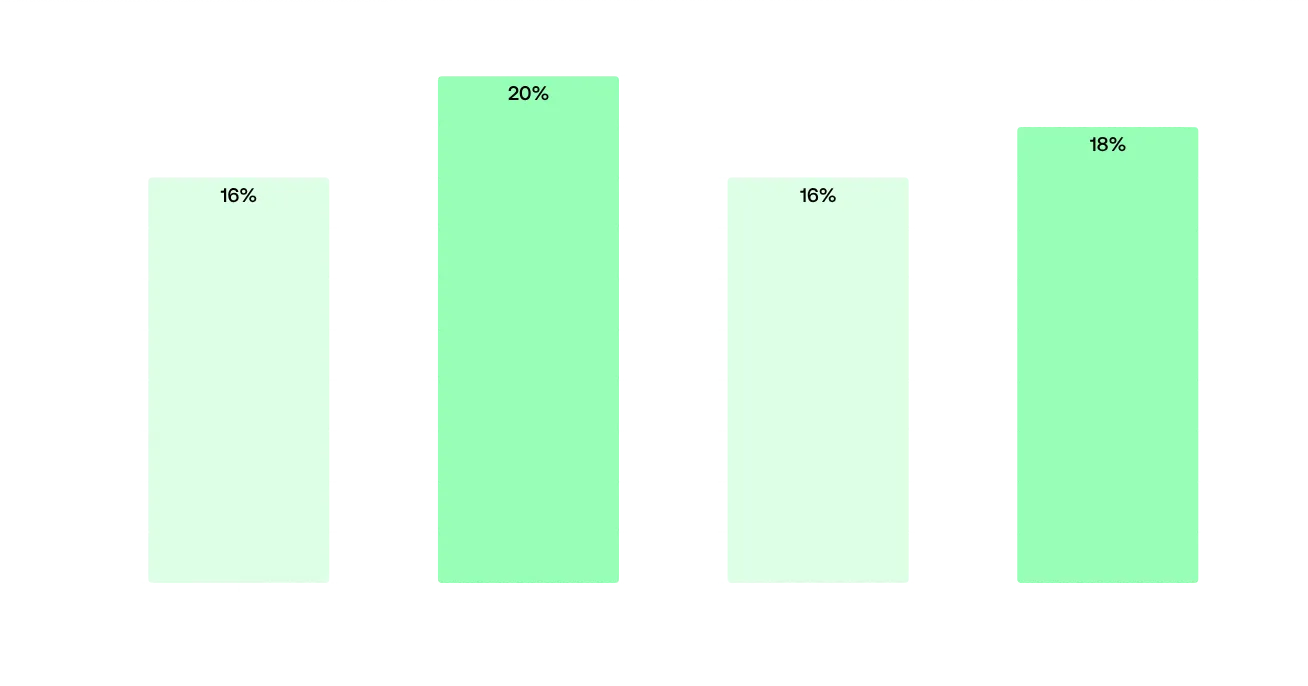 Image 10 - Percentage of SSL certificates with bad practices based on employee size
Image 10 - Percentage of SSL certificates with bad practices based on employee size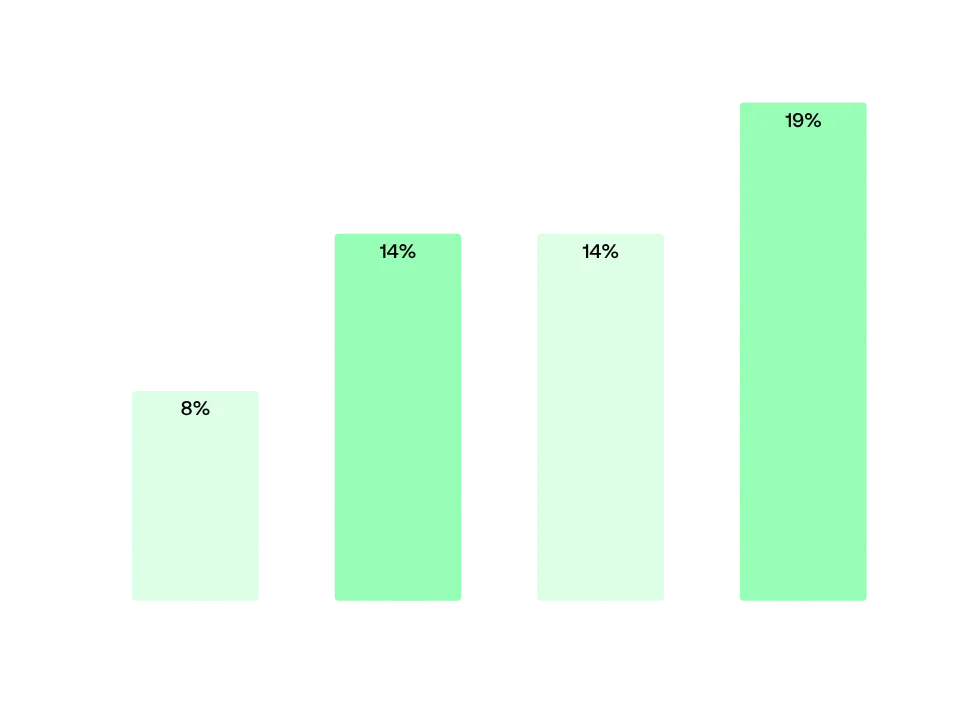 Image 11 - Percentage of SSL bad practices by asset bracket of the company
Image 11 - Percentage of SSL bad practices by asset bracket of the companyFor vulnerability management, you need to automate everything so that you can very quickly, the first day or the zero day that the vulnerabilities are found, start to close them and by the end of the day or by the end of the hour, be able to be firm that you've covered that base.
Another concerning situation identified, which may increase the risk of cyberattacks, stems from the fact that approximately 47% of web servers expose information about their version and software. When exposed, this information can be used to exploit vulnerabilities associated with it and ease the work of cybercriminals, as they can quickly look up known CVEs and vulnerabilities of these web servers.
As with SSL certificates, we found that as the number of assets increases, the percentage of exposed web servers also increases, following a consistent trend. Companies with 10,000+ employees had 77% of their web servers exposing configuration information, while smaller companies with 201-500 employees had 23%. However, it’s important to note this figure for 10,000+ employees is largely driven by Swisscom.
This trend is largely driven by a small number of very large operators whose extensive infrastructure includes many exposed servers. The 10,001+ employee bracket is heavily skewed by outliers; excluding the top offenders, the exposure rate drops significantly, suggesting the issue is concentrated rather than systemic across all large Telecom operators.
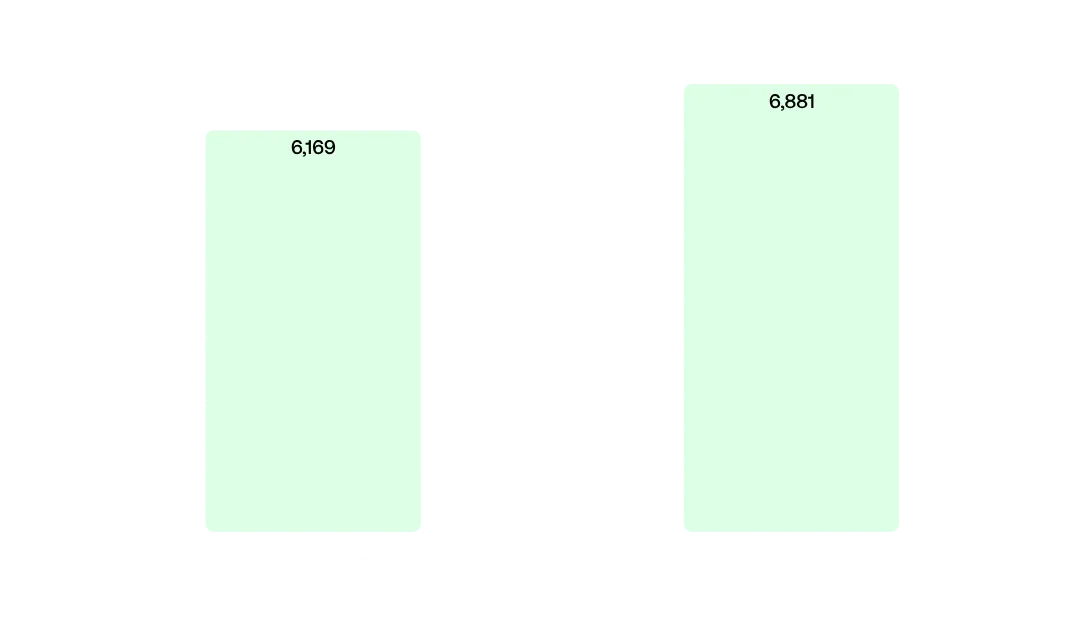 Image 12 - Number of web servers with exposed configurations
Image 12 - Number of web servers with exposed configurations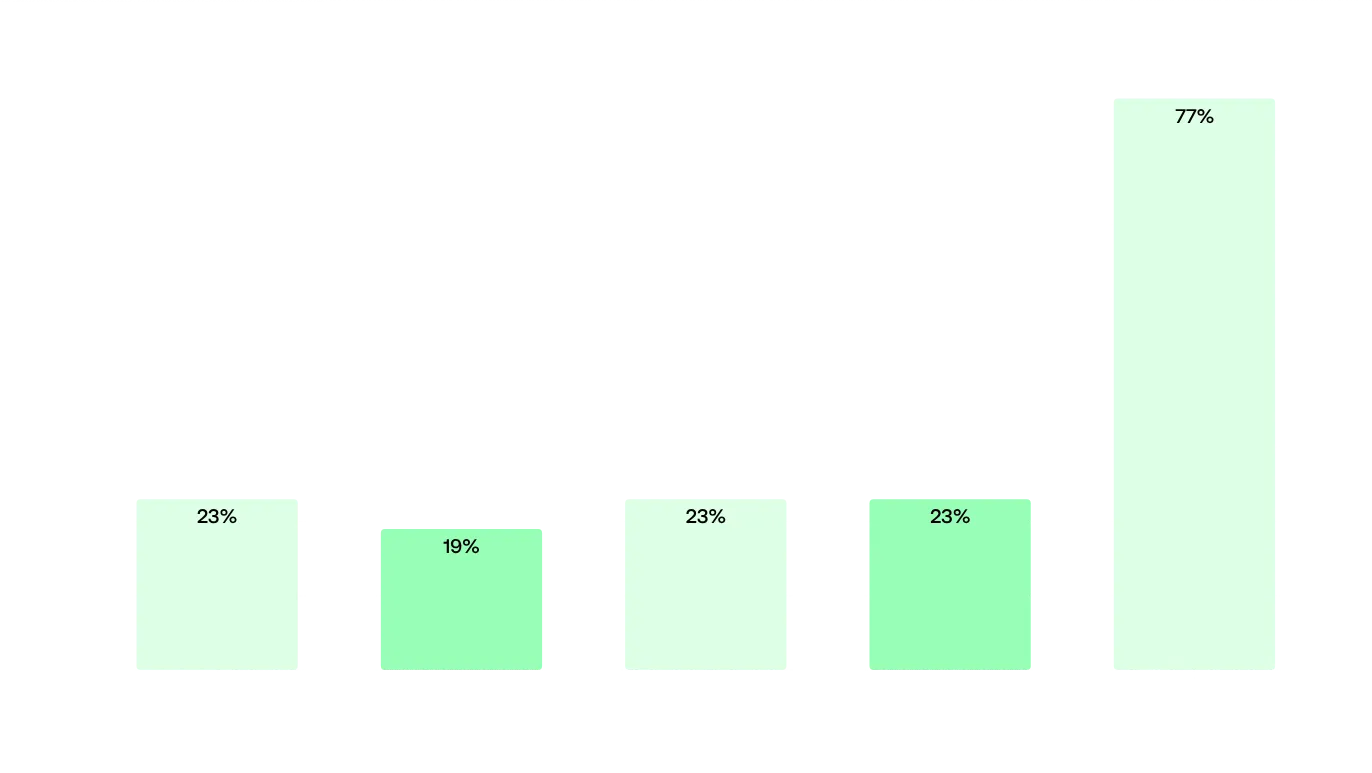 Image 13 - Percentage of web servers with exposed configurations by employee size
Image 13 - Percentage of web servers with exposed configurations by employee size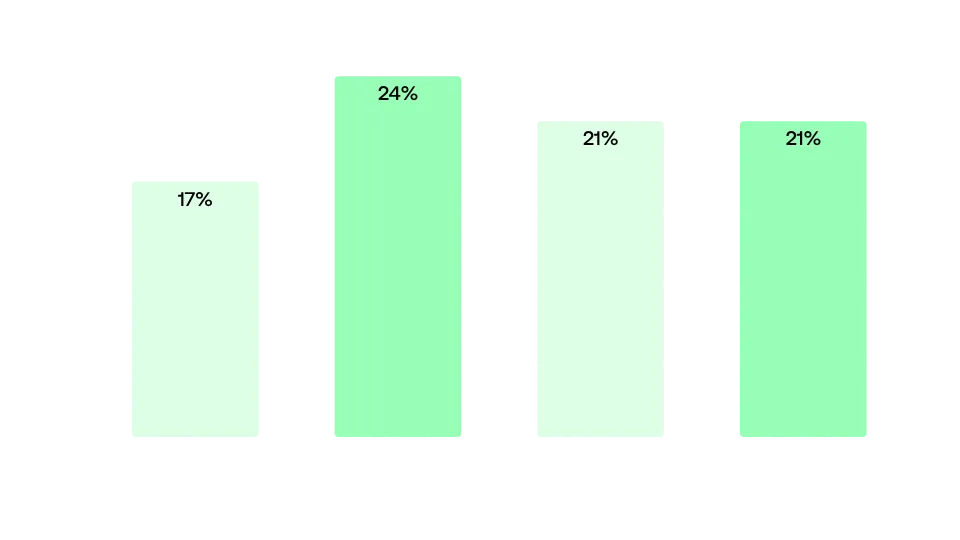 Image 14 - Percentage of exposed web server configs by asset bracket of the company
Image 14 - Percentage of exposed web server configs by asset bracket of the companyAnalysis by Country
An interesting analysis to be made is a breakdown by country. As previously mentioned, the United Kingdom has the most assets, with over 8,300 assets belonging to British companies. France takes a distant 2nd place, with 6,087 assets, followed by Switzerland with 5,576. Smaller countries, like Latvia, Cyprus, or Croatia, occupy the bottom of the table with fewer than 200 assets each.
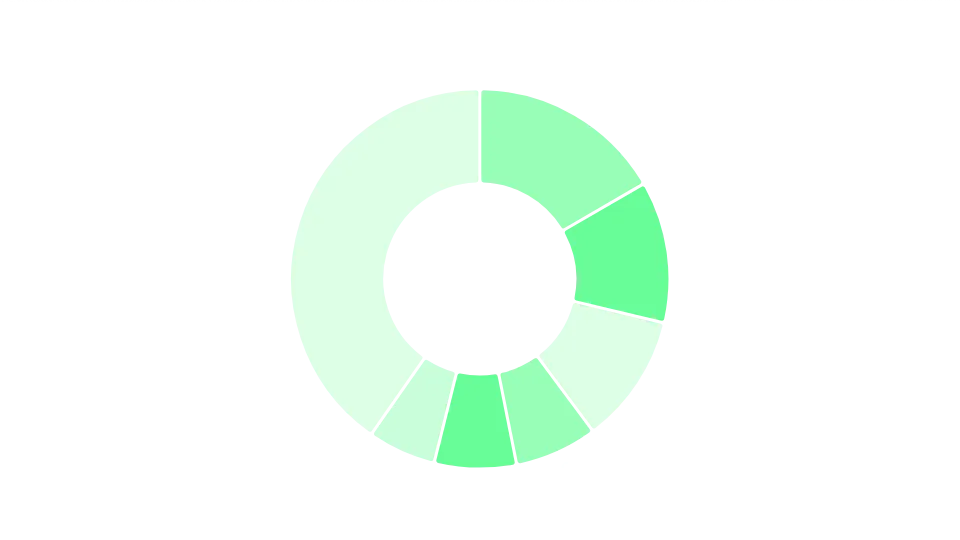 Image 15 - Distribution of assets per country
Image 15 - Distribution of assets per countryLooking at which countries have the most weaknesses, Switzerland stands out dramatically for having the worst practices for SSL certificates, at 90.5%, though this is driven primarily by a single large operator. Excluding this outlier, Malta (38.0%) and France (33.6%) had the worst SSL practices. As for exposed webservers, Estonia led with 72.1% of its servers revealing configuration information, followed by Croatia at 48.1%.
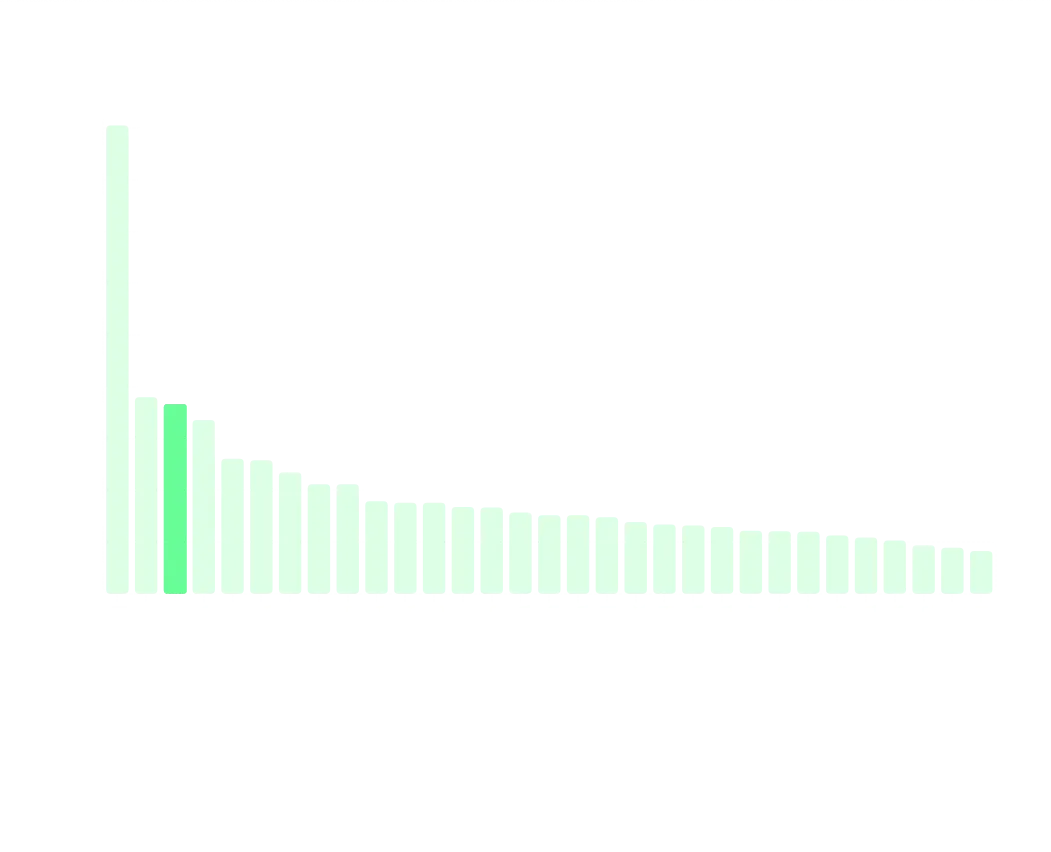 Image 16 - Percentage of SSL bad practices by country
Image 16 - Percentage of SSL bad practices by country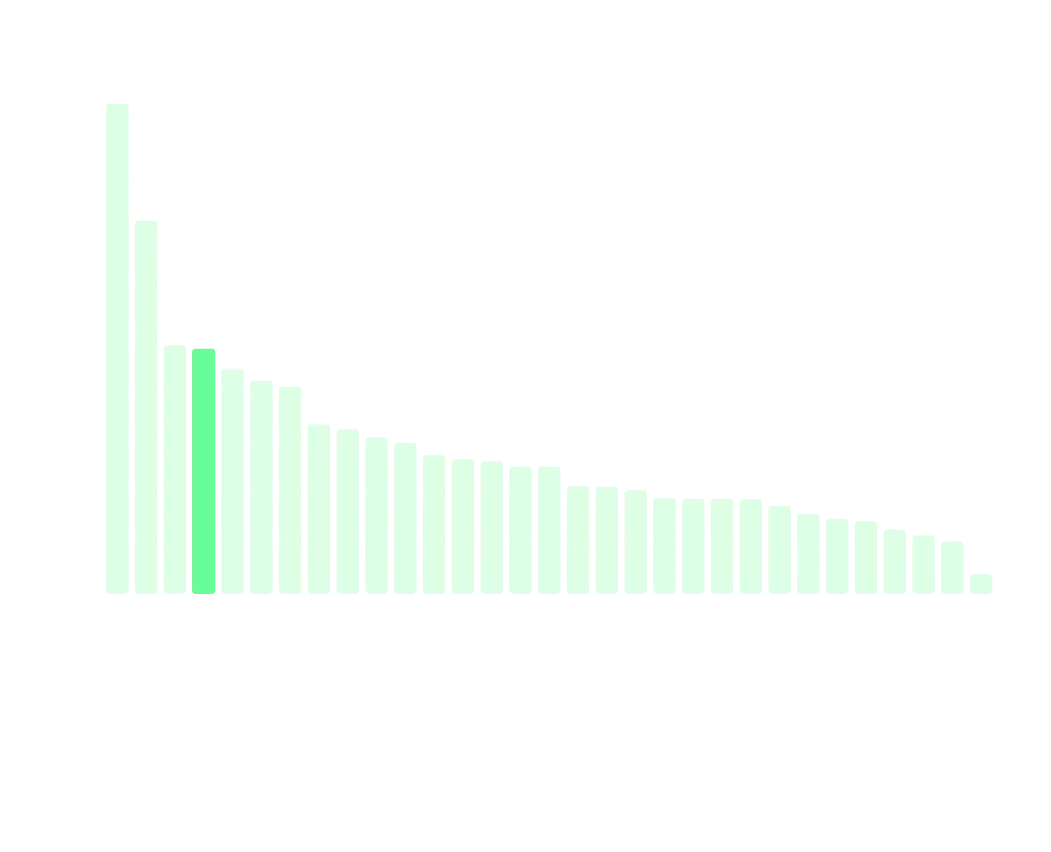 Image 17 - Percentage of exposed web servers configurations by country
Image 17 - Percentage of exposed web servers configurations by countryAnalysis by Asset Importance
We also dove into the importance of assets being used and their weaknesses. Assets vary by importance, depending on their impact of business operations in case of a breach. An email server, or an asset containing critical business information, would obviously be more impactful to the organization in case of a breach.
That being said, we found 1,452 assets we deemed important - API endpoints, email servers, admin dashboards, VPNs, portals, etc - and in these, we found several weaknesses. 19% of important assets had exposed web server configurations, and 3.3% had SSL bad practices. Webmail assets had concerning weaknesses, with 12% exposing their configs and 4% having SSL bad practices.
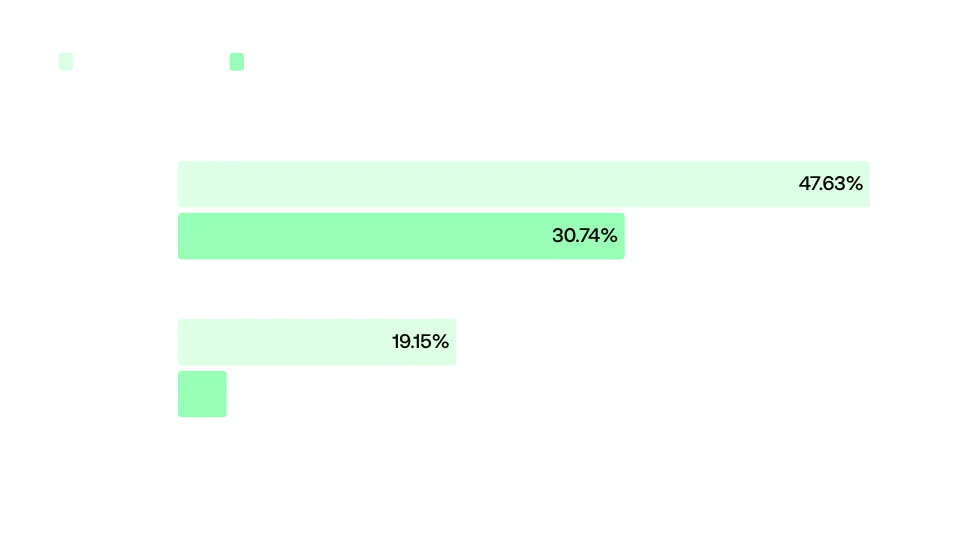 Image 18 - Exposed Web Server Configurations and SSL bad practices by asset importance
Image 18 - Exposed Web Server Configurations and SSL bad practices by asset importanceIt’s important to note that, despite these gaps in security, critical assets still show a better security posture compared to non-critical assets. 47% of non-critical assets exposed their web server configuration files, and 31% displayed SSL bad practices. Companies are clearly prioritizing their most important assets, but there is significant room for improvement across the board.
Many of these issues could be fixed by implementing proper Attack Surface Management (ASM) tools, which would map these assets and maintain security teams posted on how their infrastructure is growing. Combined with AI Pentesting, they could find out which weaknesses and vulnerabilities exist in their assets as they appear.
Analysis of AI Pentesting Data
By testing multiple Telecom organizations, often with hundreds or thousands of assets under scope, we’re able to collect information on the overall trend regarding vulnerabilities in the sector.
Some of the most common CVEs we see in Telecom are CVE-2023-48795, CVE-2024-2473, and CVE-2020-26836. These are impactful under the CVSS system, with scores ranging from 5.30 to 6.10, highlighting that even with extensive security teams and policies, CVEs can show up.
This often happens due to the massive infrastructure and complexity of Telecom organizations, together with the fact that it's simply impossible for a human-only team to keep up with all the code changes, new CVEs, and testing requirements.
Source: cvedetails.com
As for impact, CVE-2023-20198, CVE-2019-11510, CVE-2025-55182, CVE-2020-3952, and CVE-2017-7269 are among the most impactful vulnerabilities found in Telecom. These are highly impactful vulnerabilities, with devastating consequences for business if exploited - reinforcing the need for the rapid results provided by AI pentesting.
Source: cvedetails.com
Conclusions and Recommendations
The findings of this report paint a concerning picture of the cybersecurity posture of European Telecom companies. With an average of 85 exposed assets per organization (and significantly more for larger enterprises) the attack surface available to cybercriminals is substantial and growing. This expansion, combined with the widespread use of common web infrastructure technologies and security misconfigurations, creates an environment ripe for exploitation.
Five critical vulnerabilities stand out across our analysis:
First, visibility gaps remain pervasive. Over 37% of SSL connections display bad practices, and 47% of web servers expose sensitive version information (both figures skewed by a few large outliers). These are basic hygiene issues that persist because organizations lack complete visibility into their attack surfaces. This mirrors industry research showing that between 40 to 60% of attack surfaces are unknown to security teams. You cannot defend what you cannot see.
Second, critical assets are insufficiently protected. Our analysis identified 1,452 high-importance assets, such as API endpoints, email servers, admin dashboards, VPNs, and portals, with notable weaknesses. Webmail showed concerning exposure, with 12% exposing configurations and 4% running SSL bad practices. These are precisely the assets that, if compromised, would cause maximum business disruption and data loss.
Third, the vulnerability landscape is accelerating faster than organizations can respond. Our AI pentesting data reveals multiple high-severity CVEs actively present in Telecom infrastructure, including critical CVSS 10.0 vulnerabilities. With Time-to-Exploit now averaging -1 days, CVE disclosures up 16% in 2025, and the increasing tempo as evidenced by Claude Mythos, traditional periodic pentesting approaches are fundamentally inadequate.
Fourth, large organizations play a key role in eliminating the digital divide. Smaller companies are most vulnerable, and by having large organizations test their third parties and enforce strong cybersecurity standards, they can at the same time protect themselves, creating a “group immunity” effect. Not to mention the critical nature of Telecom, which is the cornerstone of entire economies.
Fifth, the Telecom sector faces an AI-accelerated threat landscape that will intensify in 2026. Security practitioners observe that AI enables attackers to scale and personalize social engineering campaigns while conducting sophisticated automated pentesting. Vivian Mura, CTO at Orange Cyberdefense, notes that attackers are using AI to speed up malware development, a trend also confirmed by Roberto Lara, Director of Cybersecurity at Vodafone Spain.
The recent attacks on major European Telecom operators such as Orange, TalkTalk, or Free Mobile demonstrate that these are not theoretical risks. They are active, costly realities.
Recommendations
Based on these findings, European Telecom organizations should prioritize the following actions:
- Move beyond point-in-time assessments to continuous discovery and testing of all exposed digital assets, including third-party and supply chain connections. Implement a Continuous Threat Exposure Management (CTEM) program with Attack Surface Management (ASM), Adversarial Exposure Validation (AEV) and Pentesting as a Service (PTaaS).
- Deploy autonomous, AI-powered penetration testing. Traditional annual or quarterly pentests cannot keep pace with modern development cycles and the velocity of new vulnerabilities. Continuous, event-driven testing triggered by code changes, infrastructure updates, or new threat intelligence is essential.
- Address basic security hygiene immediately. Invalid SSL certificates and exposed server configurations are low-hanging fruit for attackers. Automated monitoring and remediation of these issues should be standard practice.
- Prioritize critical asset protection. Map and continuously test high-value assets—authentication systems, network management interfaces, customer portals, and administrative interfaces—with particular attention to validation and proof-of-exploitation, not just detection.
- Test third-party assets. Several high-profile breaches happened due to compromised third-parties, and industry experts reveal these are even being used for social engineering. By enforcing good security postures on their suppliers, large organizations can help create a “group immunity” effect.
- Establish or expand Bug Bounty Programs (BBPs) or Vulnerability Disclosure Programs (VDPs). Enable the security research community to help identify vulnerabilities before malicious actors exploit them.
The correlation between company size, revenue, and security posture suggests that cybersecurity investment scales with resources—but it shouldn't take a breach to prioritize security. Smaller companies in our sample showed higher vulnerability rates per asset, indicating they face disproportionate risk relative to their defensive capabilities.
The European Telecom sector stands at a critical juncture. Attack surfaces are expanding, threat actors are accelerating, and the margin for error continues to shrink. Organizations that embrace continuous, autonomous security testing—combining AI speed and scale with human expertise—will be positioned to discover and remediate vulnerabilities before they become breaches. Those who rely on periodic assessments and reactive measures will continue to appear in breach headlines.
The choice is clear: evolve security practices to match the threat landscape, or accept that a breach is not a question of if, but when.
Don’t wait for the attack.
Secure Your Future with Ethiack
If you're still unsure convince yourself with a 30-day free trial. No obligation. Just testing.
